You may have security measures like surveillance cameras, alarm systems and locked cash drawers in place to prevent break-ins and theft in your store, but have you considered whether your point-of-sale (POS) system is secure? Whether through a physical break-in or a virtual one, a thief may target your POS system for the sensitive data it holds. The most valuable data to criminals is your customers’ payment information. An insecure POS system can expose your customers to credit card theft and can cause irreparable damage to your company’s reputation. We’re going to look in more detail at why you need a POS system and how you can keep your customers’ data secure so your business can grow and thrive rather than being brought down by a data breach. If you’re looking for the most secure POS system out there, the POS+ from National Retail Solutions (NRS) is the way to go.
With a semi-integrated approach, the POS and card reader still communicate, but the POS is not privy to any payment data. This marries the advantages of a disconnected and a fully integrated approach and leaves the negative of each behind. When your POS system and card reader are semi-integrated, thieves will be sorely disappointed if they target your POS and discover your customers’ data is not stored in the system.
Why You Need a Secure POS System for Your Store
No business owner wants to mishandle their customers’ payment information, but even if you think you’re doing your due diligence, your POS system could be letting you down. Many POS systems today are vulnerable to malware that steals credit card data. ZDNet explains that much of the problem is due to companies using legacy systems with vulnerabilities that are difficult to patch. Malware is not obvious and can continue affecting your POS for a long time. Earl Enterprises, which includes restaurants such as Planet Hollywood and Earl of Sandwich, discovered malware that was compromising their payment card processing systems after the malware had been active for nearly 10 months. This incident affected around 100 restaurants and is just one example of a news-worthy POS security breach. The news tends to feature security breaches that affect larger businesses, but for every one of these instances, there are many others that target small businesses. Security breaches can hurt your company’s reputation and finances. This is why it is so critical to have a secure POS. This is not an aspect of your business where you want to cut corners. When you’re shopping for a POS, you may be more concerned about finding a model that offers the pricepoint or features you’re after. While there are many factors to consider when choosing a POS system, you want to make sure security is one of them. Find out how secure a POS system is before you buy it.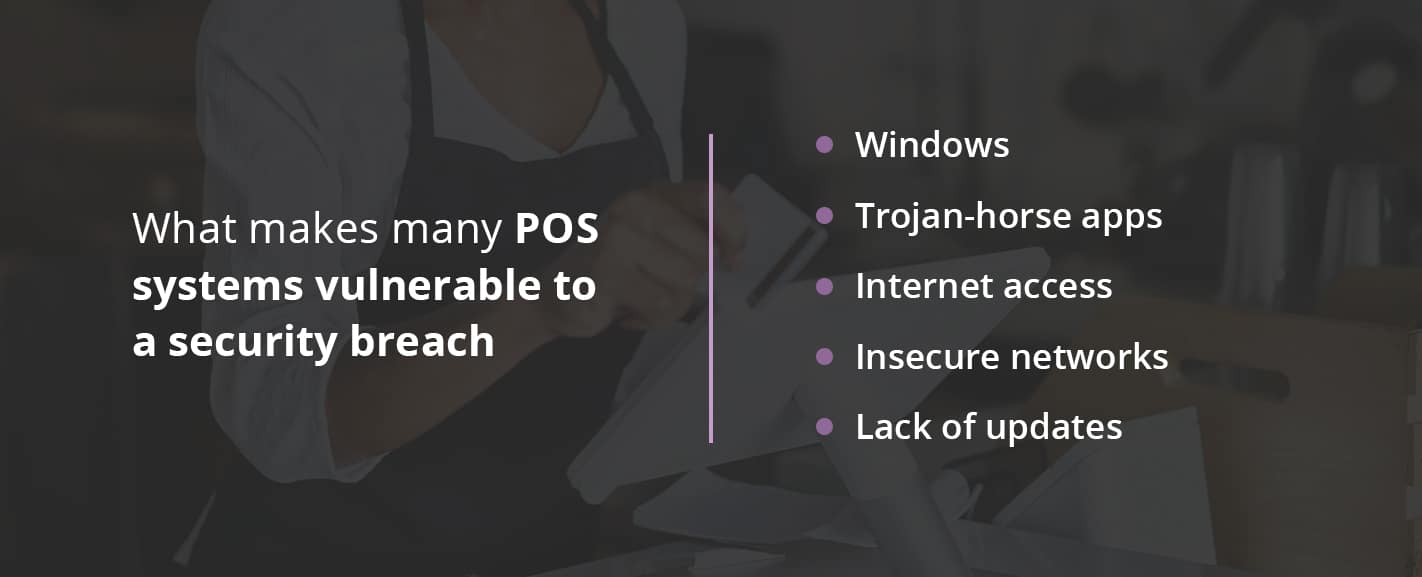
What Makes Many POS Systems Vulnerable to a Security Breach
When malware gets onto a POS system, it can access the system’s memory to collect data and send it to a remote server. Malware can make it onto POS systems in different ways, just as it can make it onto your personal laptop or phone — through email attachments, malicious links and Trojan-horse apps, for example. Here are some of the ways many POS systems open themselves up to security breaches:- Windows: Many POS systems today run on Windows, meaning they are vulnerable to the same problems a standard Windows computer is. It isn’t that Windows is inherently insecure. The issue is in the fact that Windows is a choice target for hackers since it’s such a common system. This is one reason why you should look for a POS system that has its own operating system. If you have a POS that uses Windows, make sure you install antivirus.
- Trojan-horse apps: Rather than a computer or a computer-like terminal, some stores use a tablet or even a mobile phone and simply download a POS app. These devices are also at risk if they have any other apps installed in addition to the POS app. Trojan-horse apps can masquerade as something harmless like a game but can actually have a malicious function, as well, or harvest sensitive data from your POS system.
- Internet access: Another issue with POS systems that function like standard computers or tablets is that they allow employees to surf the web, check email or play games when they aren’t busy ringing up customers. Even if you have told employees not to use the POS system for anything except work-related activities, it only takes one employee opening a phishing email or clicking on a bad link to put your POS system and its data at risk.
- Insecure networks: Yet another security risk is when your POS system is connected to WiFi or a cellular network. This connection may seem harmless enough, especially if your WiFi is password-protected, but connections like these have been shown multiple times to have weaknesses. A much safer alternative is for a POS system to be connected via Ethernet only. This protects your POS from the vulnerability of being on a more accessible network.
- Lack of updates: Since any type of technology has vulnerabilities and since the methods hackers find to infiltrate POS systems and other online systems are continually changing, system updates are critical. Operating systems and software can be improved and shored up with each update, but for some systems, updates are few and far between. Cloud-based software allows the POS company to update your system automatically, which tends to mean those valuable updates are far more frequent.
How POS Systems Handle Payment Processing Data
We’ve focused on how data can be stolen from a POS system, but we should also talk about how that data gets there in the first place. POS systems can hold data relating to a store’s inventory, employee schedules and more. In most cases, this is not the data people are interested in stealing. Instead, it is your customers’ payment information that is so attractive to criminals. If they can get a person’s credit card information, they can use that information to make fraudulent purchases or can sell each credit card’s information. Even with security developments like EMV chipped credit cards, stealing credit card information continues to be a lucrative business for cybercriminals. Payment processing can be a bit complicated to understand, but when it comes to security, the important thing to understand is what data makes it onto your POS. There are three basic scenarios:- Disconnected: In some cases, the POS is not actually involved in the payment processing at all. The card reader device does not communicate with the POS and functions completely independently. Unfortunately, this setup adds steps to the checkout process and allows more room for human error. The one upside is that your POS won’t store any payment information.
- Fully integrated: Another scenario is that your card reader and POS are seamlessly integrated. This setup is much more convenient and streamlined, but it often means your POS is holding onto sensitive payment data. As we’ve seen, this is dangerous since it makes your POS system a target for theft.
- Semi-integrated: In this scenario, the POS asks the card reader device to process a charge for a certain amount, and the card reader alone deals with the credit card data. It passes the payment information on in an encrypted form to the processing network and then says whether the payment was authorized or declined. The card reader sends the authorization code and authorized amount to the POS to complete the checkout process.
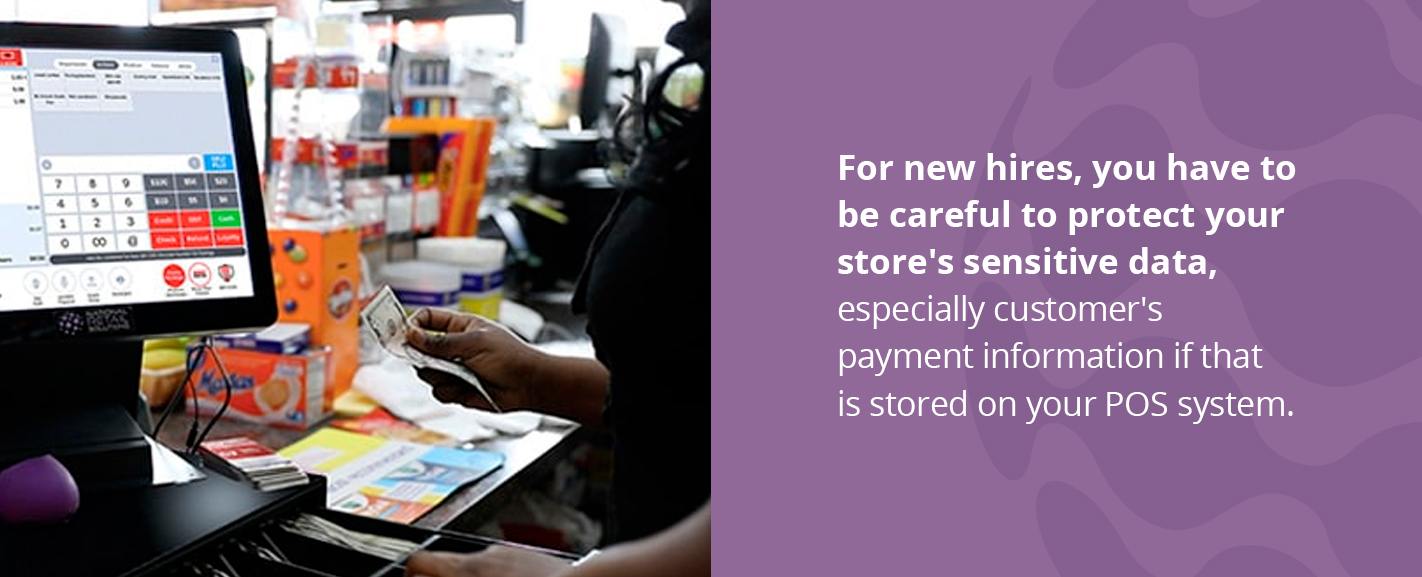
Why Internal Security Is Also Important
So far, we’ve looked at some serious external security risks that can come with some POS systems. In other words, these systems are at risk of outside criminals hacking into the system. But POS systems should also have security measures that apply to your internal team, as well. In addition to payment information, a POS system can store all sorts of sensitive information about your store, such as financial records, sales analytics and employee data. If all your employees have the same unfettered access to your POS system as you do, you could be making your store vulnerable to internal security issues. This may not be much of a concern if you have longtime employees you trust implicitly. But especially for new hires, you have to be careful to protect your store’s sensitive data, especially customer’s payment information if that is stored on your POS system. A great solution is a POS system that allows you to set user logins and special permissions for each user. You want to be able to limit the data, features and settings an employee can access so you don’t have to worry about an internal security breach or even a mistake that can be avoided when employees can only access the aspects of the POS system they need to perform their duties on the job.
How a Secure POS Can Help You Grow Your Small Business
Securing your customers’ and your store’s data helps you avoid a data breach. You may have seen some stories in the news of major retailers, restaurants and other businesses suffering the consequences of their POS systems being breached. These incidents can severely hurt a company’s relationships with its customers. When customers swipe their card to make a purchase at your store, they’re putting their confidence in your business to keep their sensitive payment information safe. When your POS system doesn’t protect that sensitive data, customers will see your business as responsible for putting them at risk. In some cases, data breaches can result in massive lawsuits that can cost your business dearly. When you’re careful to keep your customers’ data secure, instead of hurting your relationships with customers, you can build strong, trusting relationships. For customers who are concerned about the news they’ve heard of consumers’ credit card information being stolen, you can explain how your POS system will keep their information secure. It’s important to note that any online system could have minor vulnerabilities, but some POS systems will have far more security measures built-in than others to keep data protected.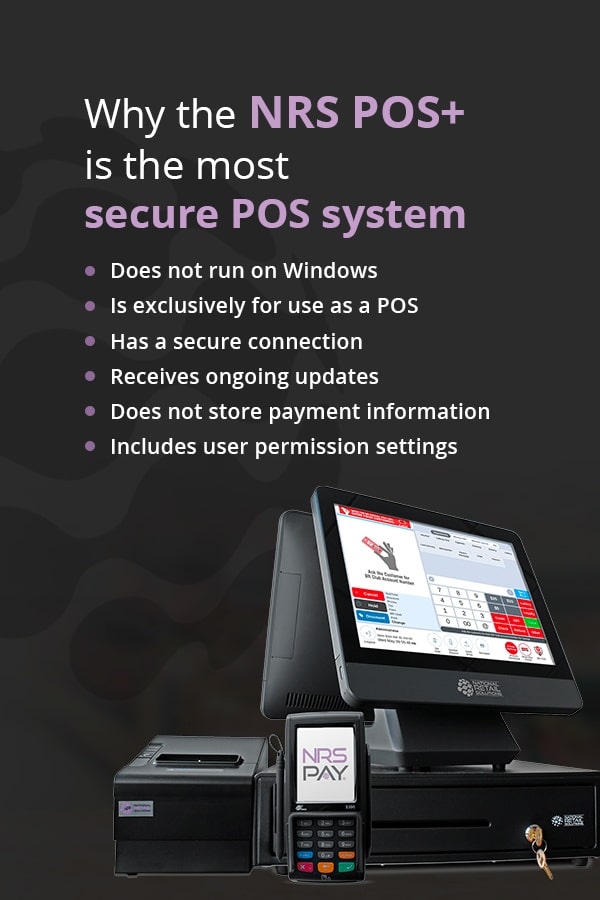
Why the NRS POS+ Is the Most Secure POS System
It should be clear now why security is a critical aspect of any POS system. If you’re looking for a secure POS system for your small business, the POS+ from NRS is an ideal choice. The POS+ is an exceptionally secure POS system because it:- Does not run on Windows: For one, the POS+ does not run on Windows or another major operating system. This automatically protects it from many common vulnerabilities that other POS systems experience.
- Is exclusively for use as a POS: Because the POS+ uses dedicated POS terminals that do not double as standard computers or tablets, you don’t have to worry about threats from the internet, email or Trojan-horse apps infiltrating the system.
- Has a secure connection: The POS+ is a cloud-based system, but it does not connect to WiFi. It is connected via Ethernet only, behind a Natted router. This means the network your POS system is on won’t compromise its security.
- Receives ongoing updates: A huge advantage of the POS+ being cloud-based is that we can update your system as needed from our remote location. This means if any vulnerabilities or glitches are ever detected, they will quickly be shored up.
- Does not store payment information: A major security feature the POS+ offers is secure payment processing through the semi-integrated approach we described above. This means your POS will not store sensitive payment information.
- Includes user permission settings: The POS+ allows you to customize user permissions for each employee. You can designate someone as an administrator, manager or cashier and then select which features they are allowed to access.